In today's digital realm, cyber threats loom large. Businesses and individuals alike are increasingly vulnerable to online predators who seek to exploit vulnerabilities for personal gain. Protecting your sensitive information and systems requires a proactive approach, and that's where ethical hackers come in. An white hat security expert can proactively identify your weaknesses before attackers do, providing you with invaluable insights and actionable recommendations to bolster your defenses. Don't wait for a breach to occur - embrace proactive cybersecurity by hiring an ethical hacker today.
- Strengthen your defenses against cyberattacks
- Gain valuable insights into vulnerabilities
- Receive expert guidance on security improvements
Detecting Fraud: Comprehensive Investigation & Evidence Gathering
Suspicions of cheating require a meticulous and comprehensive approach. A thorough investigation should encompass various stages, beginning with a clear framework of the suspected actions. Investigators must diligently gather evidence from diverse sources, including statements, documents, electronic records, and physical items. Maintaining chain of custody is paramount throughout the process to guarantee the legitimacy of the collected evidence.
- Examining the gathered evidence requires expertise and a critical eye. Investigators must distinguish patterns, inconsistencies, and potential connections that can shed light on the depth of the cheating.
- Documenting all findings in a clear and concise manner is essential for building a strong case. A detailed report should outline the investigative process, evidence collected, analysis conducted, and judgments reached.
The goal of exposing cheating is not merely to discipline those involved but also to avoid future occurrences. By implementing robust investigative procedures and fostering a culture of integrity, organizations can reduce the risks associated with cheating.
Access Unseen Access: Phone Monitoring Apps for Comfort
In today's connected world, safeguarding your loved ones and belongings has never been more important. Phone monitoring programs offer a powerful way to gain hidden knowledge into the actions taking place on mobile smartphones. Whether you're a caregiver worried about your child's cyber safety or an manager seeking to monitor employee usage, phone monitoring programs can provide the peace of mind you need. These advanced software allow you to remotely observe a wide range of data, including text messages. By staying updated of what's happening on mobile smartphones, you can take effective actions to secure your business.
Suffered a Social Media Security Breach? We Can Help You Reclaim Control
Your online safety is our priority. If you've recently been struck by a platform security breach, don't worry. Our expert team is here to guide you through this difficult time. We'll work with you to analyze the breach, pinpoint any stolen data, and implement measures to strengthen your security.
- Get in touch for a free evaluation.
- We got this you regain control over your digital presence.
Shielding Your Brand Against Social Media Hackers
In today's online landscape, maintaining a strong image presence on social media is crucial. Unfortunately, this also exposes your business to potential security threats. Hackers are constantly seeking vulnerabilities to exploit accounts and disseminate harmful content. To safeguard your brand from these risks, it's imperative get more info to implement robust security measures.
- Regularly update your social media profiles with the latest software. This helps patch weaknesses that hackers could leverage.
- Implement strong and unique passwords for each social media profile. Avoid using the same password across multiple sites.
- Enable two-factor authentication (copyright) whenever possible. This adds an extra layer of defense by requiring a code from your phone or email in addition to your password.
Be vigilant about phishing attempts. Don't click on suspicious links or provide personal information through unverified platforms.
The Essential Guide to Cybersecurity Audits: Proactive Vulnerability Detection
In today's interconnected world, cybersecurity threats constantly evolve, posing a significant risk to organizations of all sizes. To mitigate these threats and protect valuable assets, it is crucial to conduct regular cybersecurity audits. A comprehensive audit enables the identification of vulnerabilities before malicious actors can exploit them.
- Certified security professionals utilize a variety of tools and techniques to evaluate your systems, networks, and applications for weaknesses.
- The audit process typically involves reviewing security policies, configurations, and logs, as well as conducting simulated attacks to identify potential entry points.
- Ahead of time addressing vulnerabilities through remediation efforts, organizations can significantly reduce their risk of a successful cyberattack.
Cybersecurity audits offer a roadmap for strengthening your defenses and ensuring the integrity of your data. Consistent audits are essential for staying ahead of the ever-evolving threat landscape.
 Danny Tamberelli Then & Now!
Danny Tamberelli Then & Now! Jake Lloyd Then & Now!
Jake Lloyd Then & Now! Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now!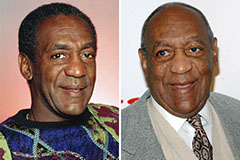 Bill Cosby Then & Now!
Bill Cosby Then & Now! The Olsen Twins Then & Now!
The Olsen Twins Then & Now!